Top security best practices in Magento and how to implement them
Imagine leaving the door open to your shop after closing or. Or not installing any security measures, such as an alarm system, in case someone tries to break into your store. You probably would not do that.
If you have an online shop, there are also some security measures you should take, to keep your shop and your customer’s data safe. In fact, it should be one of your top priorities.
Magento is a very powerful open-source platform – but as with any other platform, it is often targeted for server attacks, credit card skimming, cross-domain scripting, remote code execution, etc.
Even though there is no way to eliminate all security risks, there are steps you can take to make your shop a less likely target. This article will cover the top best practices you should follow. The article is based on our many years of experience and on Adobes security best practices guide.
Securing your Admin Panel
It is recommended that you take multiple steps to secure your admin panel. If someone unauthorized gains access to your admin, they can inject code directly into your site, for example for credit card skimming.
1. Do not use standard admin access URL
Don’t use admin logins like “admin”, or “backend”. They are easy to find as they are easy to guess. It is therefore recommended to use a custom admin URL that contains a minimum of 7 characters and is a combination of numbers, letters, and symbols. You could use a password generator to create your admin URL.
How to change the Admin Base URL in Magento2:
You can follow the Adobe Guide for changing your base URL and path here.
We always recommend a developer help you change the URL if you don’t know how to edit configuration files on the server.
2. Add Secret Key to URLs in Magento 2
To prevent CSRF attacks https://portswigger.net/web-security/csrf on your Magento backend, we recommend that you enable Secret Key for URLs.
How to enable Add Secret key to your URL on Magento 2:
Go to Stores > Configuration > ADVANCED > Admin > Security > Add Secret Key to URLs
This will add a secret key/value pair at the suffix
3. Limit password lifetime and set forced password change
It is very important that every single user that has access to your admin panel keeps good password hygiene – this means having a unique, difficult-to-guess password and updating it often.
We recommend using a password generator to generate unique passwords, such as roboform, lastpass, or 1password. It is recommended that a password contains a minimum of 7 characters and consists of letters, symbols, and numbers.
We also recommend you limit the lifetime of admin users’ passwords and change the Password Change to be forced.
To change the admin password settings, Go to Stores > Configuration > ADVANCED > Admin > Security >
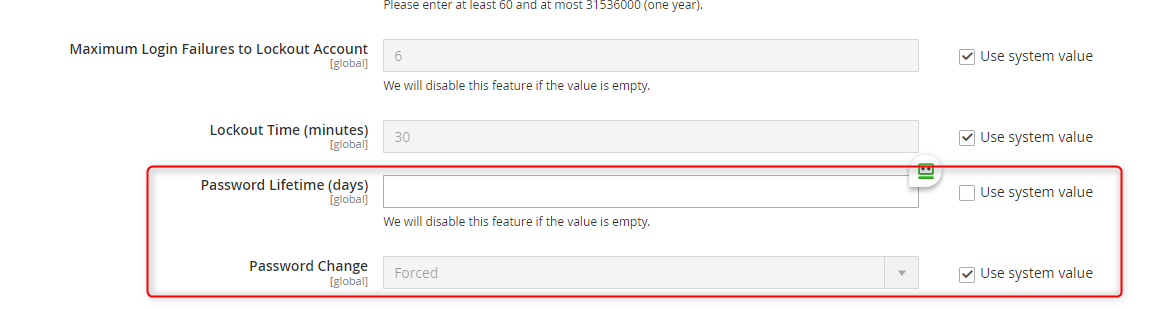
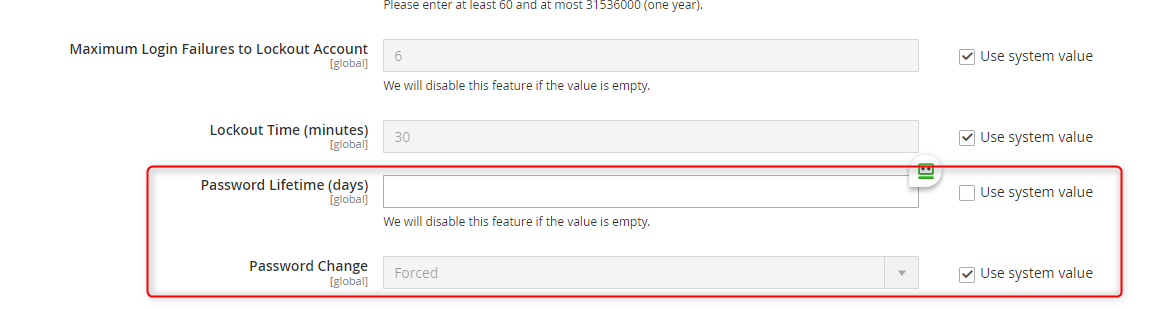
Set the desired days a password should be valid for in Password Lifetime (days) and make sure the Password Change field is set to Forced. Now admin users will be prompted to update their password when they try to log in after the password expires.
4. Add CAPTCHA in frontend and admin panel
It is highly recommended to use CAPTCHA on your site, either the Magento built-in captcha or Google reCAPTCHA. A CAPTCHA is a visual device that will ensure that only humans, not computers (bots), interact with your site.
Many times, bots will be used to overload the server with multiple requests, both to the admin panel, but even more so on Newsletter signup, create an account, contact form, etc. Not only can this put unnecessary pressure on your server load, but it can also result in thousands of spam users signing up for your newsletter that you then need to spend time cleaning up, or even worse your payment plan with your email marketing provider could become more expensive.
How to add CAPTCHA or Google reCAPTCHA to Magento 2:
You can see in the Adobe Magento User Guide how to configure admin and customer CAPTCHA here: https://docs.magento.com/user-guide/v2.3/stores/security-captcha.html
5. Use the latest Magento version and patches
Adobe releases new versions and security patches during the year. Each release contains multiple security fixes for know vulnerabilities. Magento is an Open-Source software, which means anyone can access the code and abuse any vulnerabilities. Luckily there is a strong community of developers that together with Adobe find and fix these. Therefore, we recommend you update as soon as you can, after a new release or patch. We wrote a bit more about the risks of being on an outdated and unsupported Magento version here.
6. Scan your Magento store for Malware
Adobe offers a free Security Tool to scan your site for known security risks, malware, and unauthorized access. You can find it here https://account.magento.com/scanner/dashboard
You can use it to monitor your site in the future once it is set up.
Why is it bad if your store is infected with malware, and what are the consequences?
- Malware can intercept a customer’s personal data (such as name, address, credit card details. Can be used for spamming, identity theft, credit card theft etc.)
- Attempt “payment diversion fraud”
- Infect your customer’s machines with malware.
Any of the above points could cause major harm to your reputation and depending on the severity and where your business is located could be expensive as well in fines and legal fees.
So, it is recommended to continuously scan and monitor for malware on your Magento shop.
7. Keep admin users’ computer safe
We would recommend anyone to keep their computers safe, but it is even more so important that anyone that has admin access to your Magento shop, keep their computer safe. This means they should scan their computer for malware/viruses, make sure they have a safe password for their computer, and refrain from clicking on any suspicious emails and links.
8. Use correct permissions on your files
Core Magento and directory files should all be set to “read only”, including app/etc/local.xml. Hackers will try to infect Magento 2 stores, which do not have these files set to “read only”, so discourage them by having the correct file permissions.
9. Use IP whitelisting for your admin
Make a list of IP addresses that can access your admin panel. This can limit “rogue connections”. In case your admin credentials get stolen, this will ensure they can’t log in using them since their IP won’t be the same as yours,
It could also be an option if you want to limit the places where your employees can log in from.
10. Remove unused 3rd party extensions
The more 3rd party extensions you have installed, the bigger chance there are for a security vulnerability to be present, especially if you are not using and updating them. For every piece of software you are using, there is a potential vulnerability, so why take the chance with extensions you are not even using?
Go through your extension list and check which ones you are using, and make sure you remove the ones that you are no longer using.
Conclusion
These are just a few of many, many steps you could take to keep your store safe. If you are unsure if your store is safe, you want to receive a review of the extensions you are using, want help checking for malware, feel free to reach out to us here at vConnect by using the contact form below or writing an email to [email protected] and we will contact you for a no-obligation quote.

